





 The Elder Scrolls IV: Oblivion
The Elder Scrolls IV: Oblivion
 The Elder Scrolls V: Skyrim
The Elder Scrolls V: Skyrim
 The Elder Scrolls: Online
The Elder Scrolls: Online
 Fallout: New Vegas
Fallout: New Vegas
 Fallout 4
Fallout 4
 Fallout 76
Fallout 76
 Mount & Blade: Warband
Mount & Blade: Warband
 Mount & Blade II: Bannerlord
Mount & Blade II: Bannerlord
 Kenshi
Kenshi
 The Witcher 3: Wild Hunt
The Witcher 3: Wild Hunt
 Cyberpunk 2077
Cyberpunk 2077
 Kingdom Come: Deliverance
Kingdom Come: Deliverance
 Minecraft
Minecraft
 Crusader Kings 2
Crusader Kings 2
 Crusader Kings 3
Crusader Kings 3
 Hearts of Iron IV
Hearts of Iron IV
 Stellaris
Stellaris
 Cities: Skylines
Cities: Skylines
 Cities: Skylines II
Cities: Skylines II
 Prison Architect
Prison Architect
 RimWorld
RimWorld
 Euro Truck Simulator 2
Euro Truck Simulator 2
 American Truck Simulator
American Truck Simulator
 Microsoft Flight Simulator 2020
Microsoft Flight Simulator 2020
 Farming Simulator 17
Farming Simulator 17
 Farming Simulator 19
Farming Simulator 19
 Spintires и Spintires: MudRunner
Spintires и Spintires: MudRunner
 BeamNG.drive
BeamNG.drive
 My Summer Car
My Summer Car
 My Winter Car
My Winter Car
 OMSI 2
OMSI 2
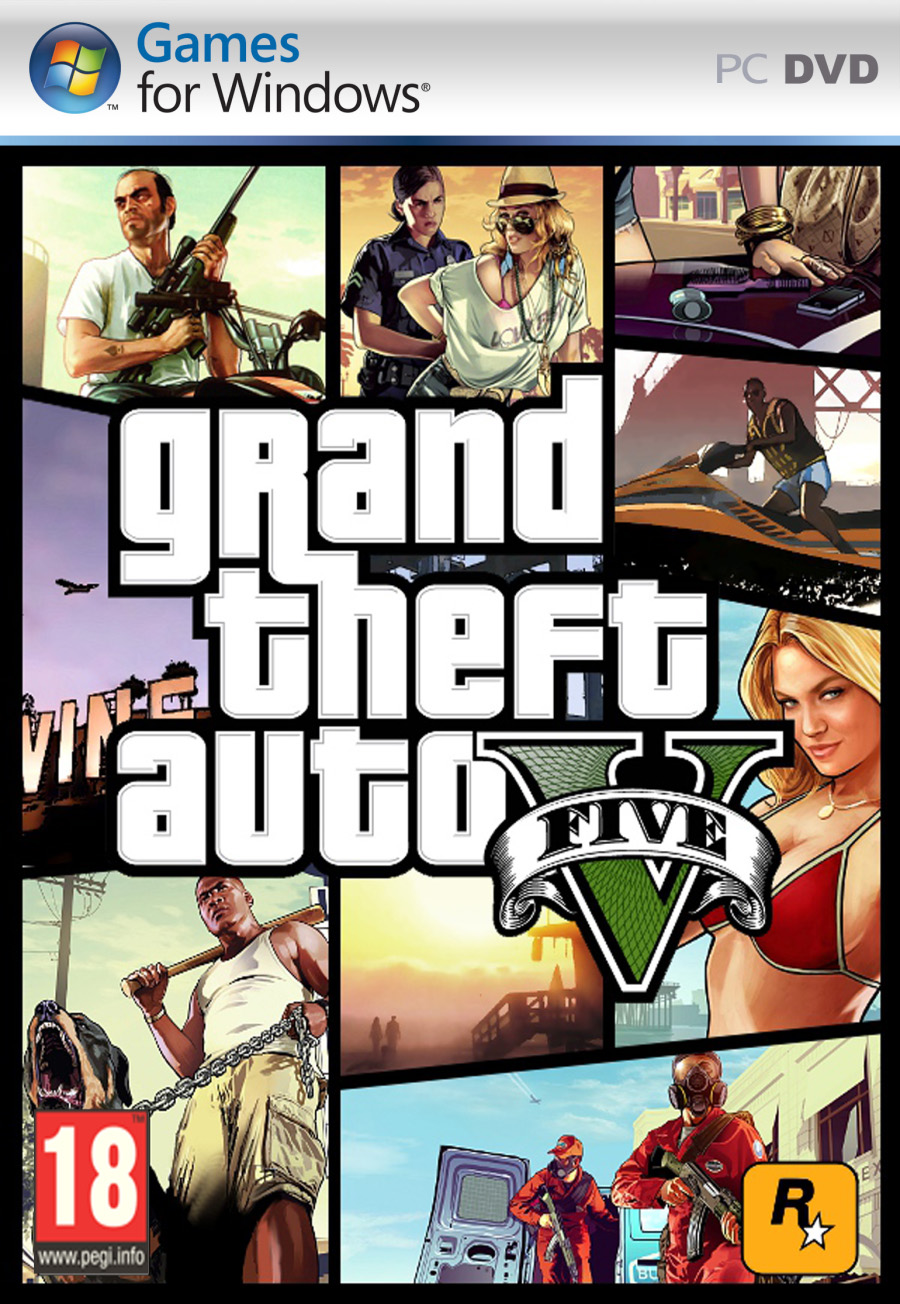 Grand Theft Auto: V
Grand Theft Auto: V
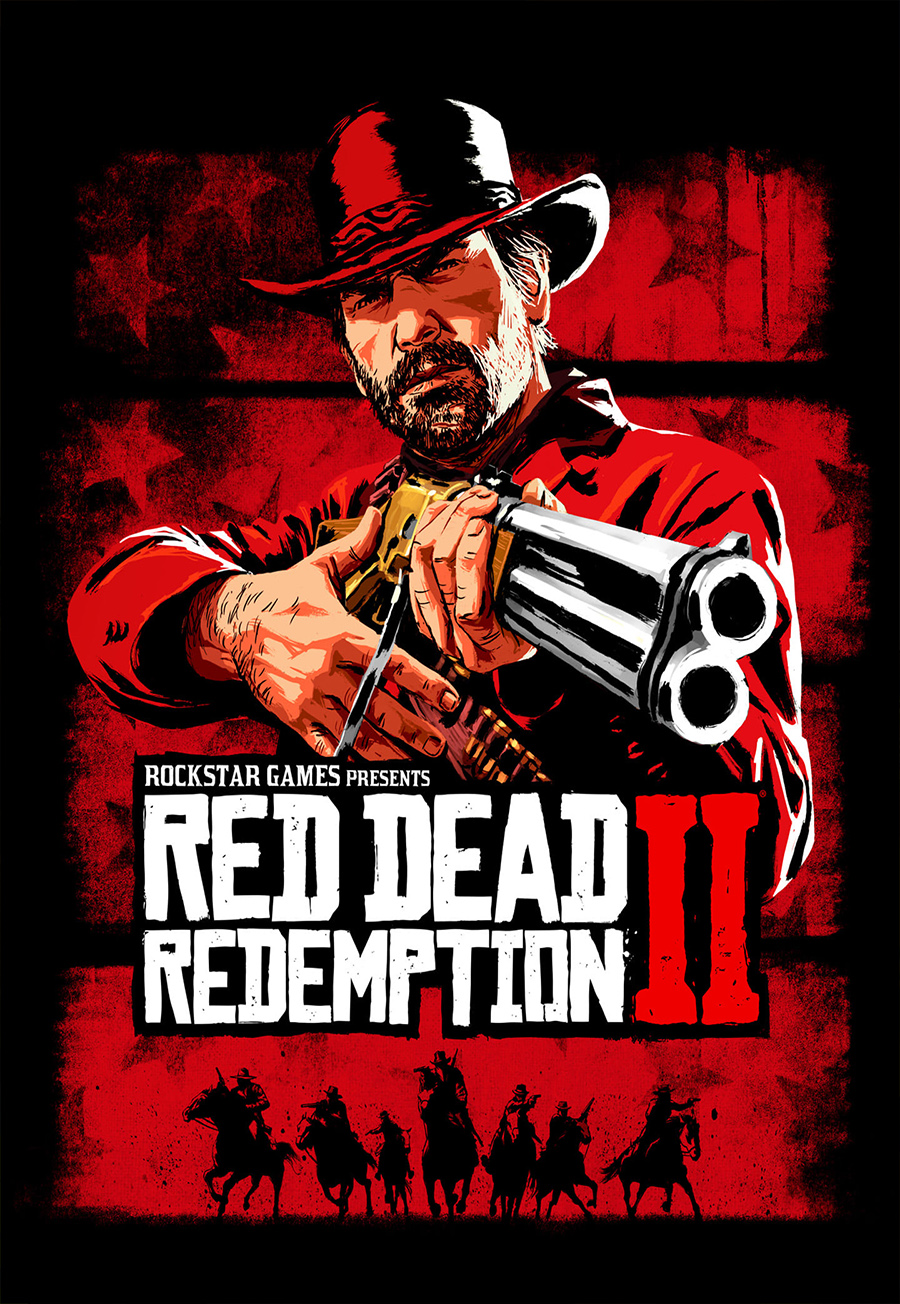 Red Dead Redemption 2
Red Dead Redemption 2
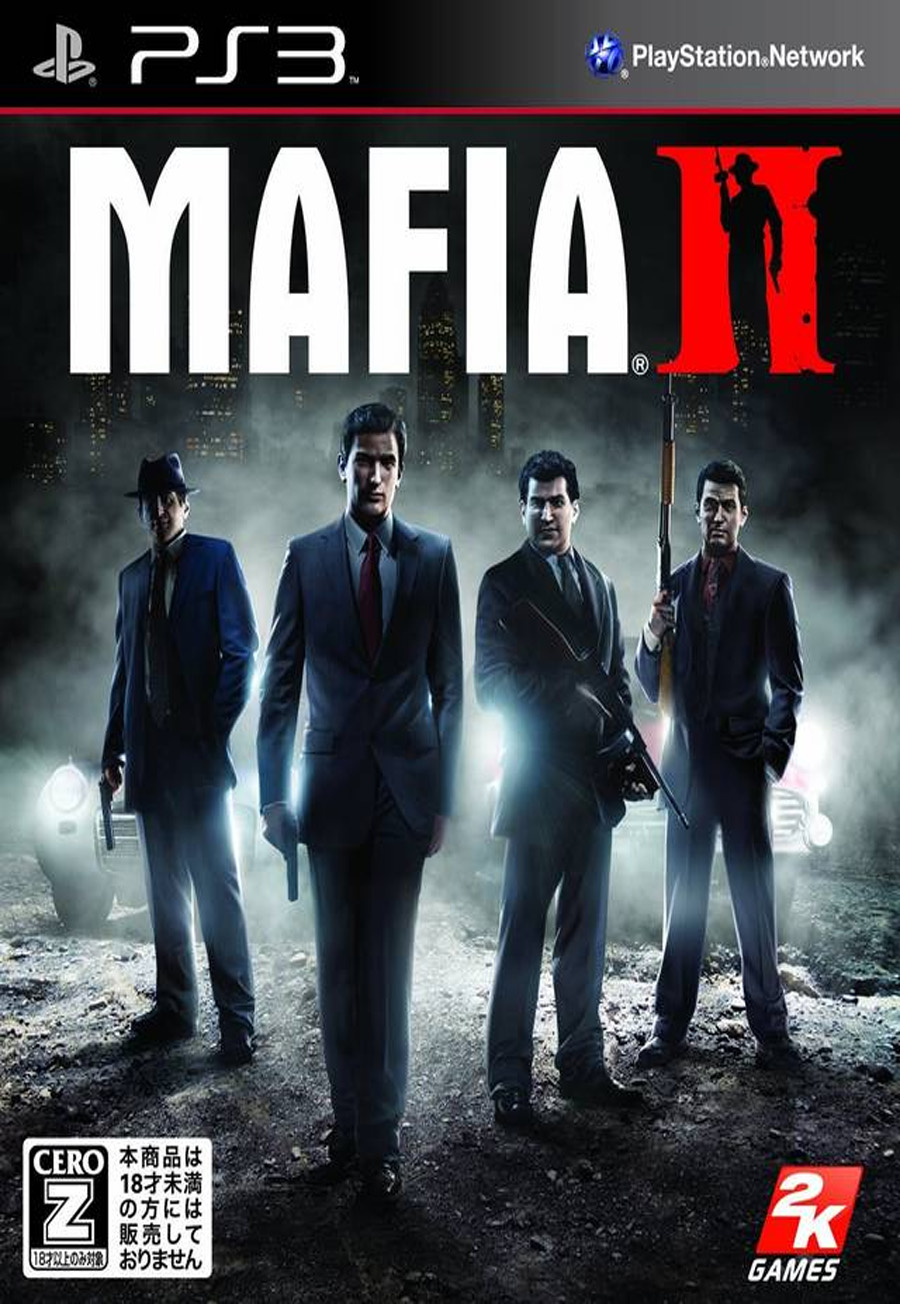 Mafia 2
Mafia 2
 Stormworks: Build and Rescue
Stormworks: Build and Rescue
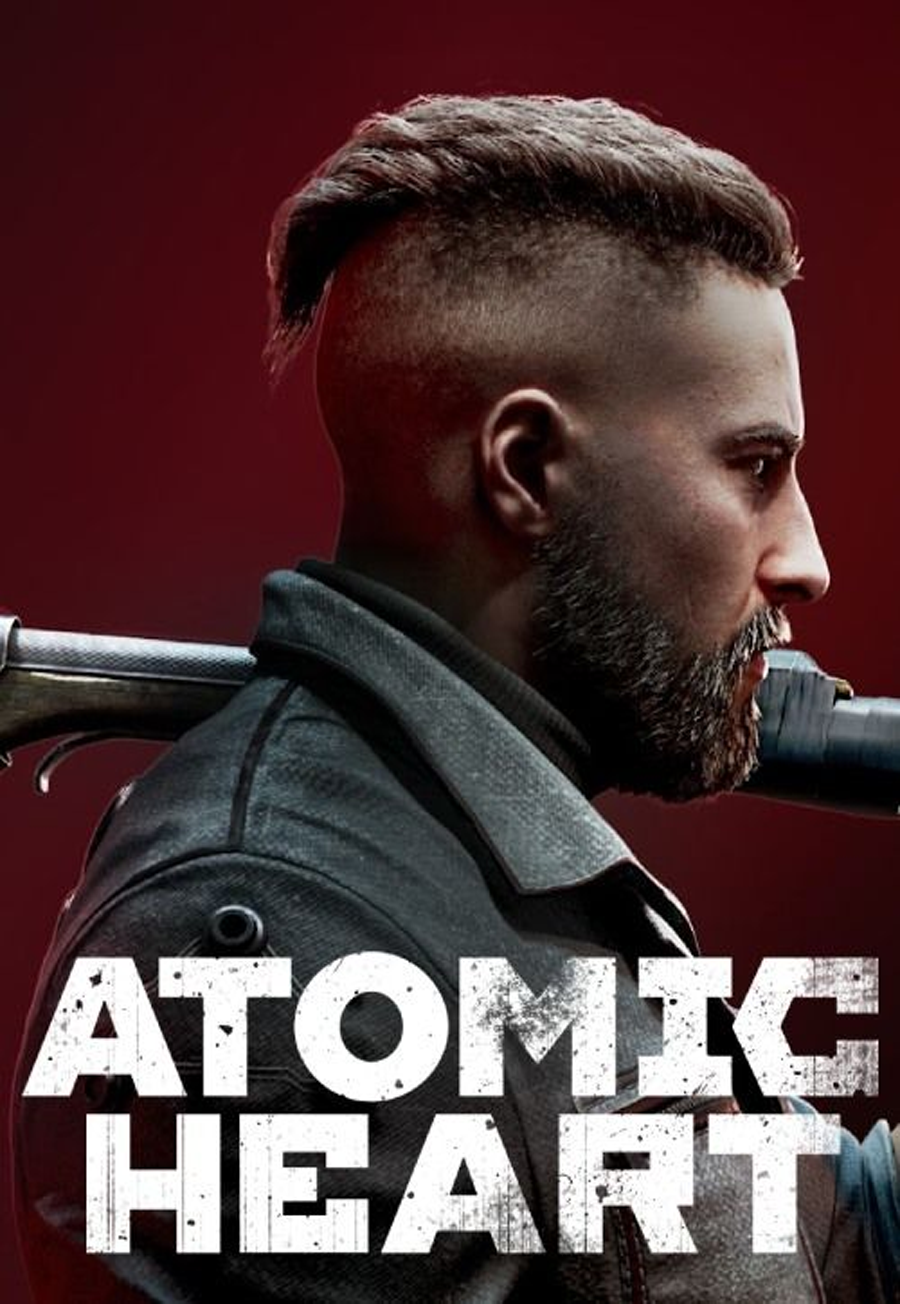 Atomic Heart
Atomic Heart
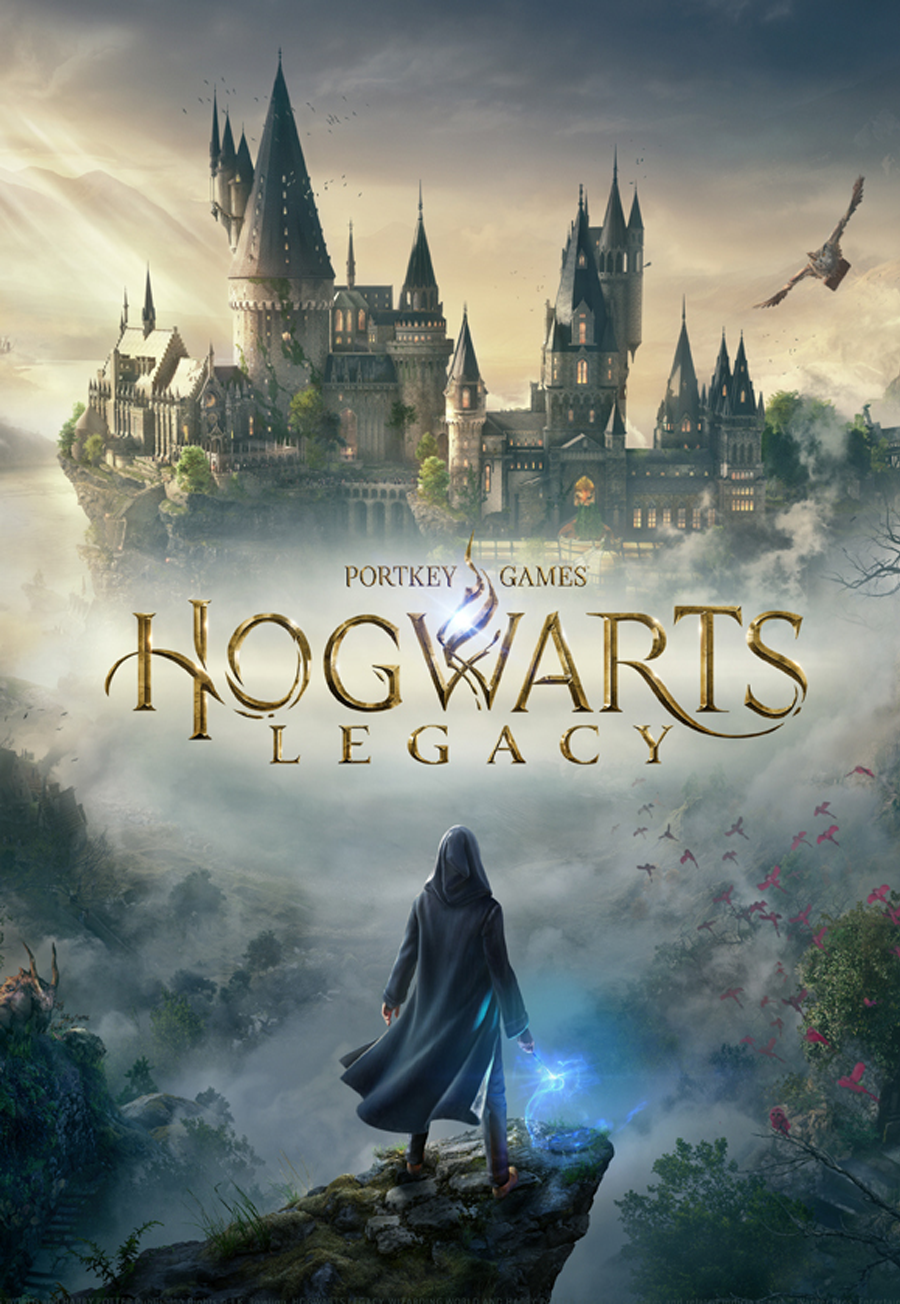 Hogwarts Legacy
Hogwarts Legacy
The Mysterious Case of Pastebin.com 8twfdyme: Uncovering the Truth**
In the vast expanse of the internet, there exist numerous platforms where users can share and access a wide range of information. One such platform is Pastebin, a popular online service that allows users to share text-based content, including code, scripts, and other types of data. Among the countless pastes created on this platform, one particular link has garnered significant attention: pastebin.com 8twfdyme. In this article, we will delve into the mystery surrounding this link and explore its contents.
The link pastebin.com 8twfdyme appears to be a standard Pastebin paste, created by an anonymous user. The contents of the paste are not immediately accessible, as Pastebin often uses a combination of encryption and access controls to protect sensitive information. However, by analyzing the link and surrounding online activity, we can infer that the 8twfdyme paste may contain sensitive or confidential data.
The mystery surrounding the pastebin.com 8twfdyme link serves as a reminder of the potential risks associated with sharing sensitive information online. While we cannot access the contents of the paste directly, online rumors and speculation suggest that it may contain sensitive or confidential data. As online users, it’s essential to be aware of these risks and take steps to protect ourselves and our organizations from potential data breaches and cyber threats.